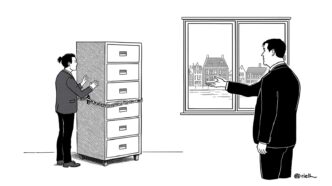
Professional services firms spent decades perfecting the art of looking trustworthy.
Mahogany furniture. Confident handshakes. The implicit promise your secrets are safe with us.
Then Nova ransomware allegedly walked into KPMG Netherlands on January 23, 2026.
Posted proof on the dark web. Set a ten-day deadline. Reminded everyone trust doesn’t encrypt data.
The irony is thick enough to audit.
The Multiplication Problem We Pretended Didn’t Exist
The mechanism nobody wanted to say out loud:
Breach one professional services firm, compromise hundreds of clients at once.
We built a business model where concentration of sensitive data is the value proposition. Financial records. Compliance documentation. Strategic plans. All sitting in one place, behind whatever security theater the firm funded between partner retreats.
The criminals figured out the math before we admitted it publicly.
Professional services saw 494 incidents in 2025. A 30% jump from 2024.
Not random. Targeting.
The Industrialization of “Give Us Money or We Publish Everything”
Nova operates like a franchise.
Distributed infrastructure. Standardized deployment. Ten-day negotiation deadlines calculated to maximize psychological pressure without giving you time to think clearly.
This isn’t some kid in a basement anymore. Ransomware became a mature criminal enterprise while we were still treating it like an IT problem.
The number of ransomware groups increased 30% in one year. From 103 groups to 134.
Watching other criminals get paid is excellent market research, apparently.
The Part Where Paying Doesn’t Even Work Anymore
Remember when ransomware groups had a reputation to protect?
When paying the ransom meant they’d delete your data and leave you alone?
Adorable.
Criminals are breaking their own promises now, asking for more even after payment. The “honor among thieves” business model collapsed faster than confidence in perimeter security.
You’re negotiating with people who have zero incentive to keep their word.
But sure, keep pretending a rational transaction is happening here.
What Controls This (Spoiler: Boring Stuff)
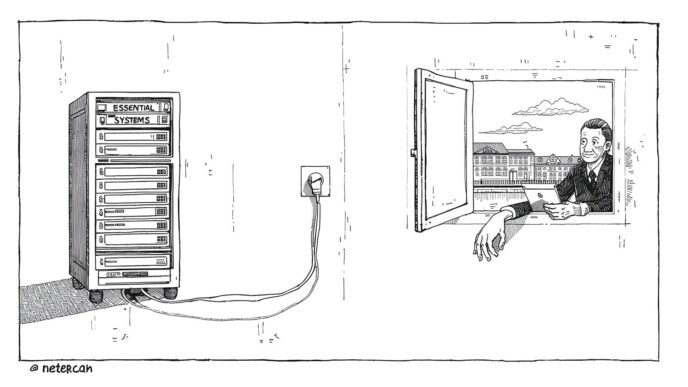
The fix isn’t sexy.
Separation of access. Proof of authorization. Incident response plans people have practiced.
You need:
- Client data segmentation working as designed
- Access logs someone reviews before the breach, not after
- Backup systems living off the main network
- Response protocols tested when there’s no emergency
The control points exist. We keep choosing mahogany furniture instead.
The Underreporting Problem Makes Everything Worse
The part worth knowing:
85% of ransomware attacks go unreported.
We’re making decisions based on visible incidents while the threat scene is six times larger than what we’re seeing.
Not a knowledge gap. Structural blindness by choice.
Every unreported breach is another firm quietly paying, another set of controls failing without anyone learning from it, another data point disappearing into silence.
The Trust Model Meets Reality
Professional services firms sell expertise wrapped in confidentiality. The entire value proposition rests on “your information is safe with us.”
One breach doesn’t cost money alone. It undermines the fundamental promise built over decades.
When financial services organizations report a 65% ransomware hit rate and $3 million average recovery costs, we’re not talking about IT incidents.
We’re talking about business model fragility.
The structure making professional services valuable is the same structure making them targets.
We either acknowledge this and build controls, or we keep pretending trust is a security strategy.
Structure is cheaper than explaining to clients why their confidential data is on a dark web leak site.
But what do we know. We’re the ones watching firms choose confidence over controls, then act surprised when criminals choose them.you don’t prove your data is segmented, backed up, and recoverable, you’re one ten-day deadline away from finding out what this costs.